6 WHAT IS COMPUTER SCIENCE AND ENGINEERING? | Computing the Future: A Broader Agenda for Computer Science and Engineering |The National Academies Press
Proceedings of the 29th annual international ACM SIGIR conference on Research and development in information retrieval: Evaluati
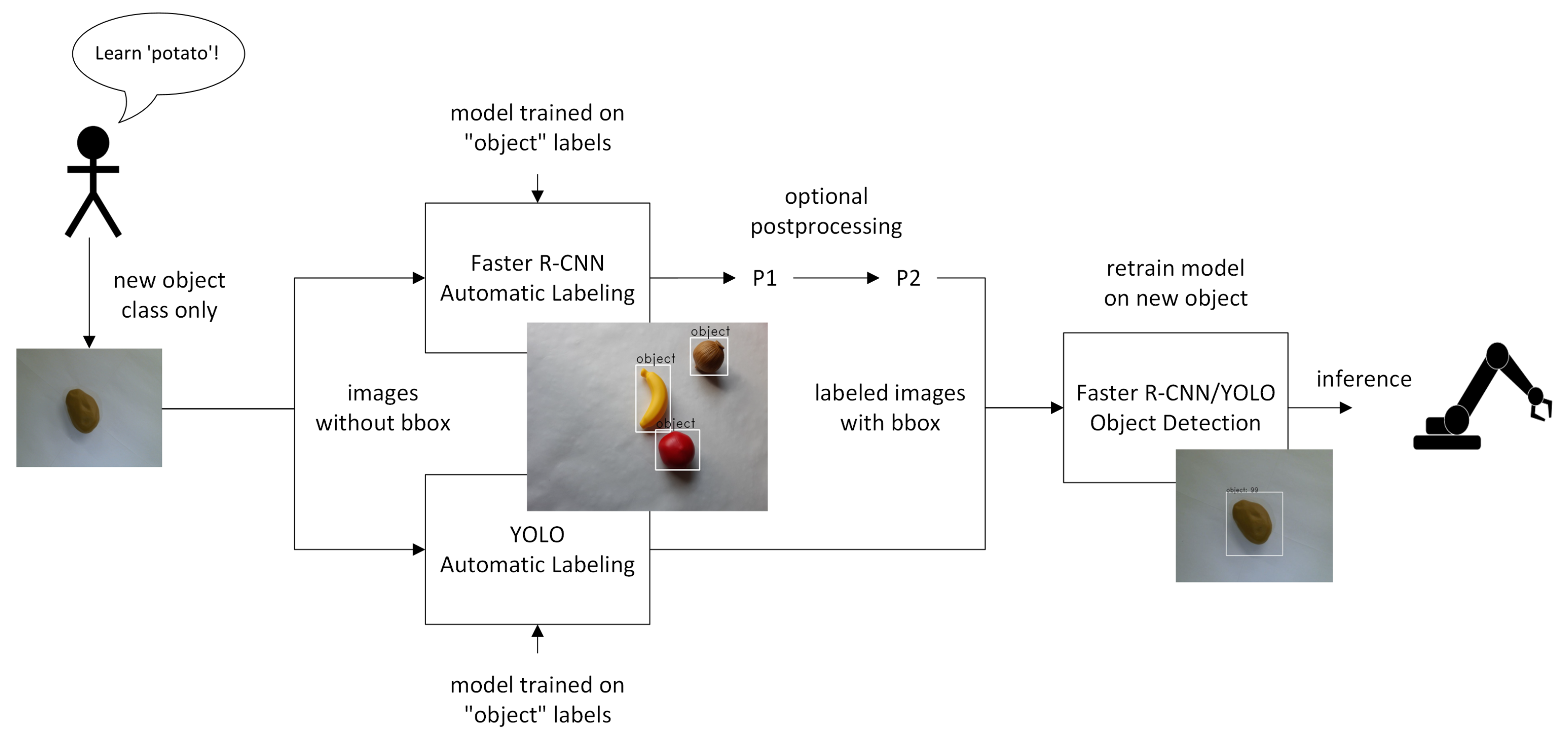
Micromachines | Free Full-Text | Automatic Bounding Box Annotation with Small Training Datasets for Industrial Manufacturing
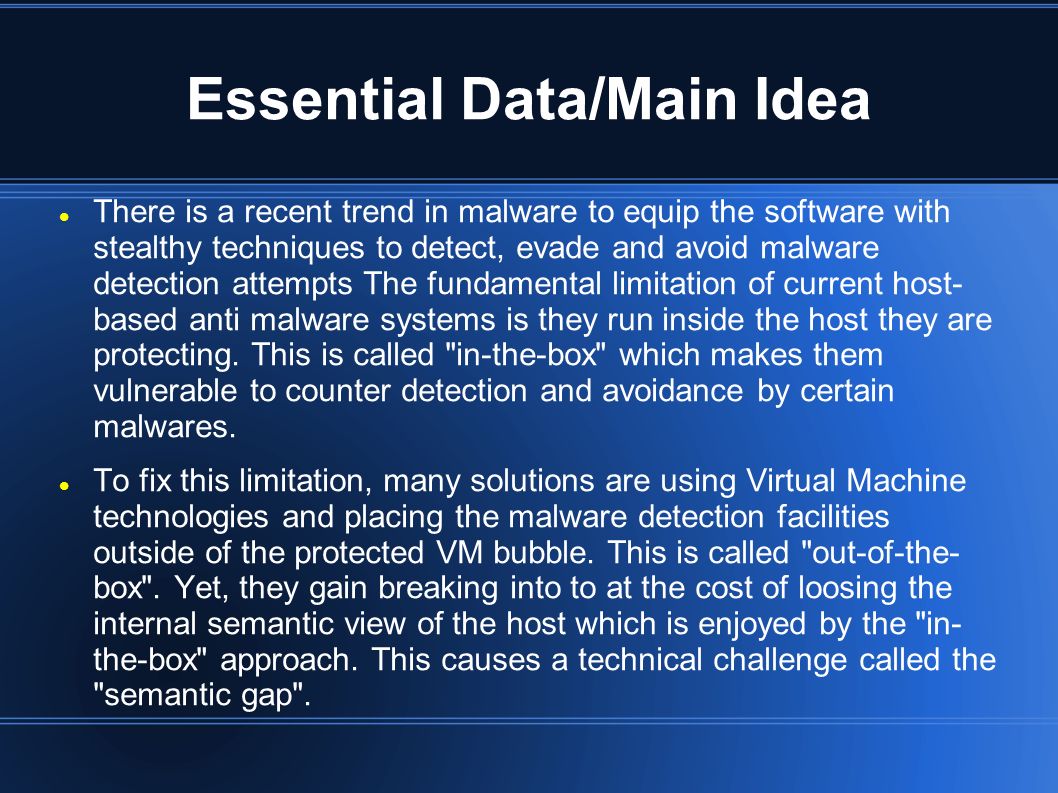
The Semantic Gap Challenge Stealthy Malware Detection Through VMM-Based “Out-of-the-Box” Semantic View Reconstruction November 2007 ACM: Association for. - ppt download
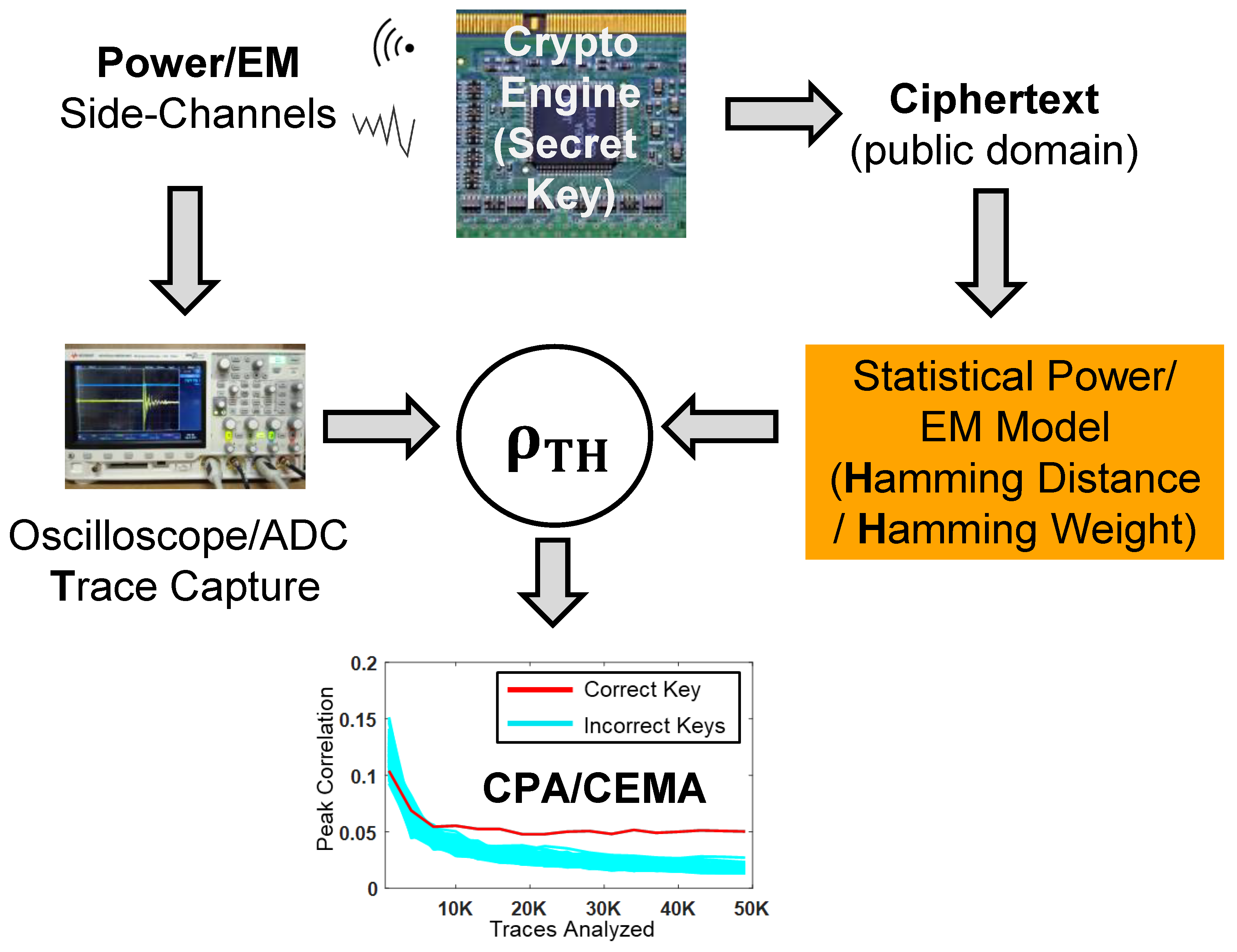
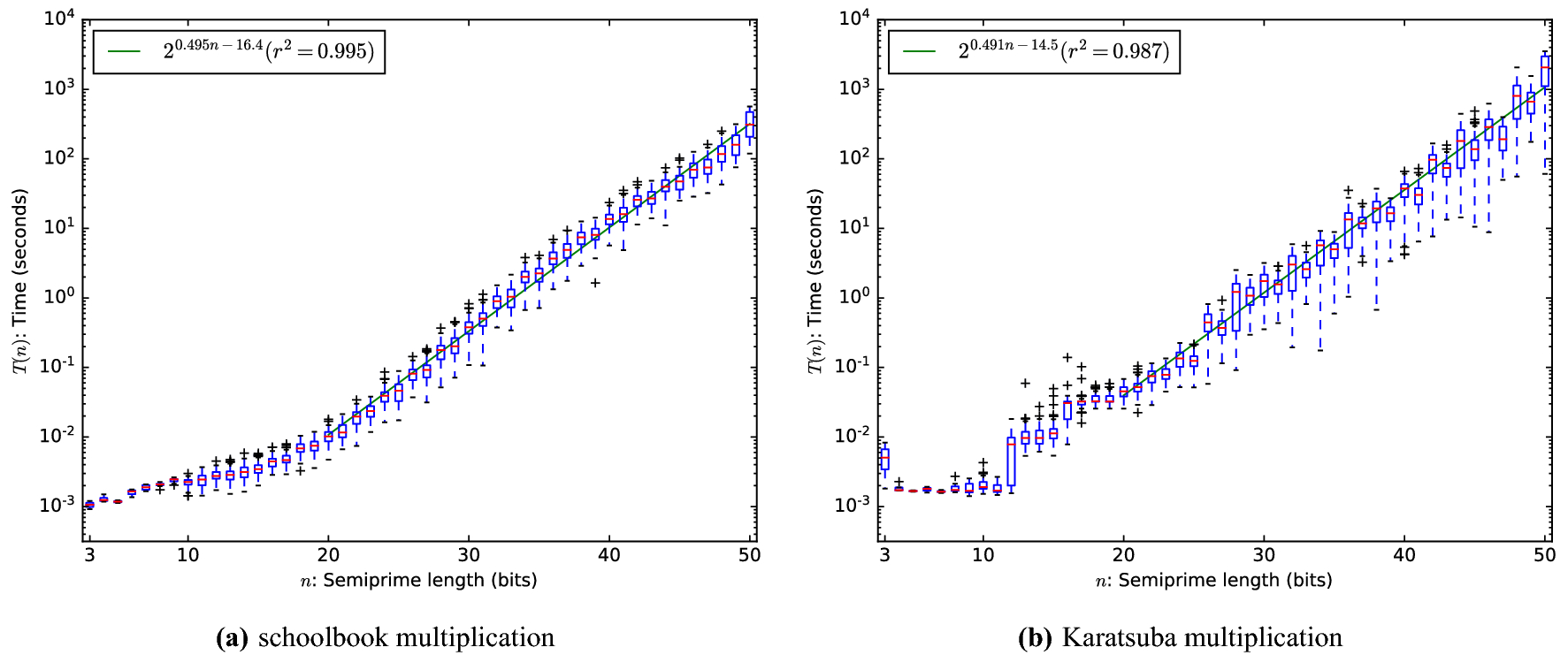
Cryptography | Free Full-Text | Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach
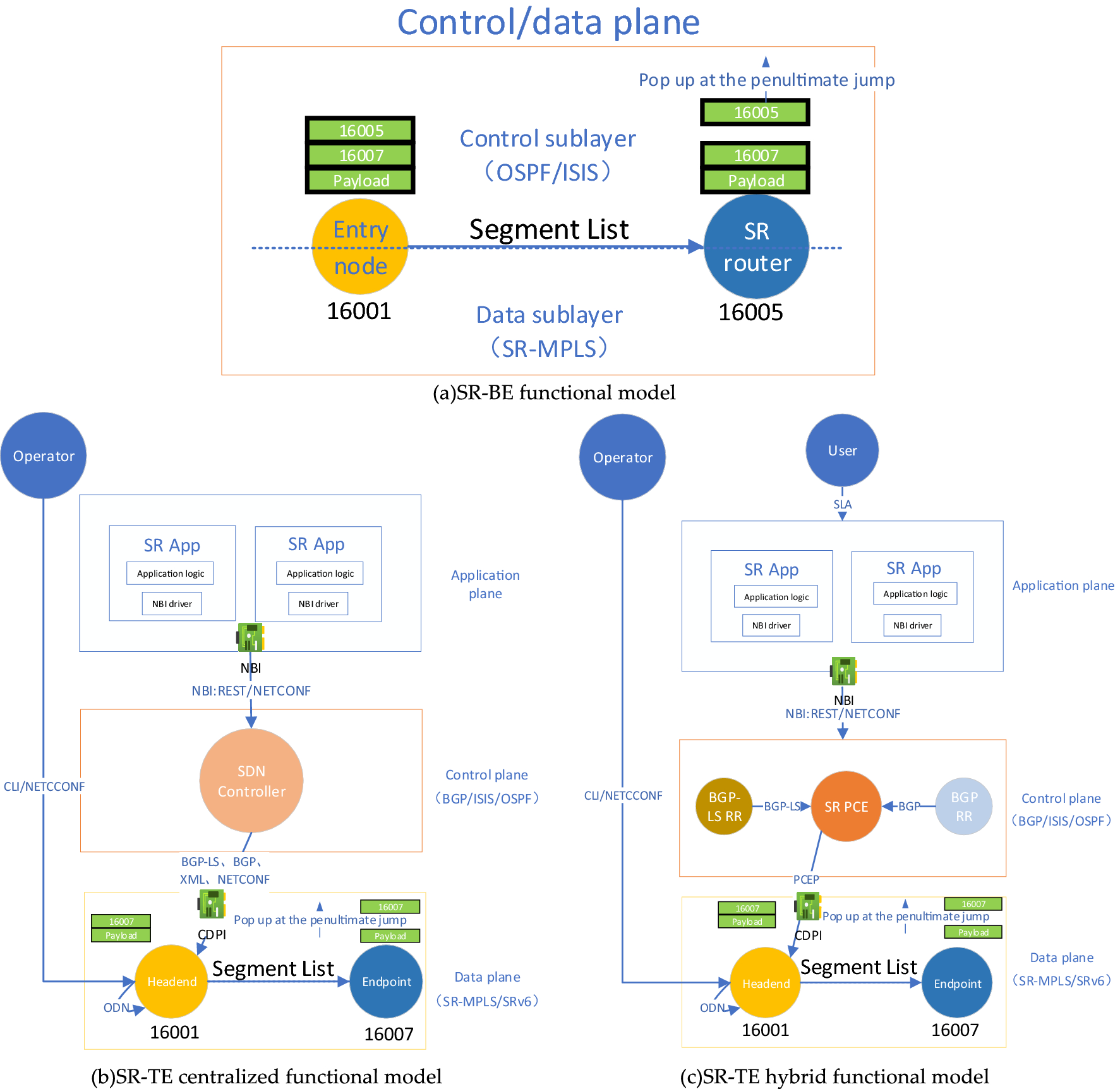
A data plane security model of segmented routing based on SDP trust enhancement architecture | Scientific Reports

A program-driven simulation model of an MIMD multiprocessor | Proceedings of the 24th annual symposium on Simulation
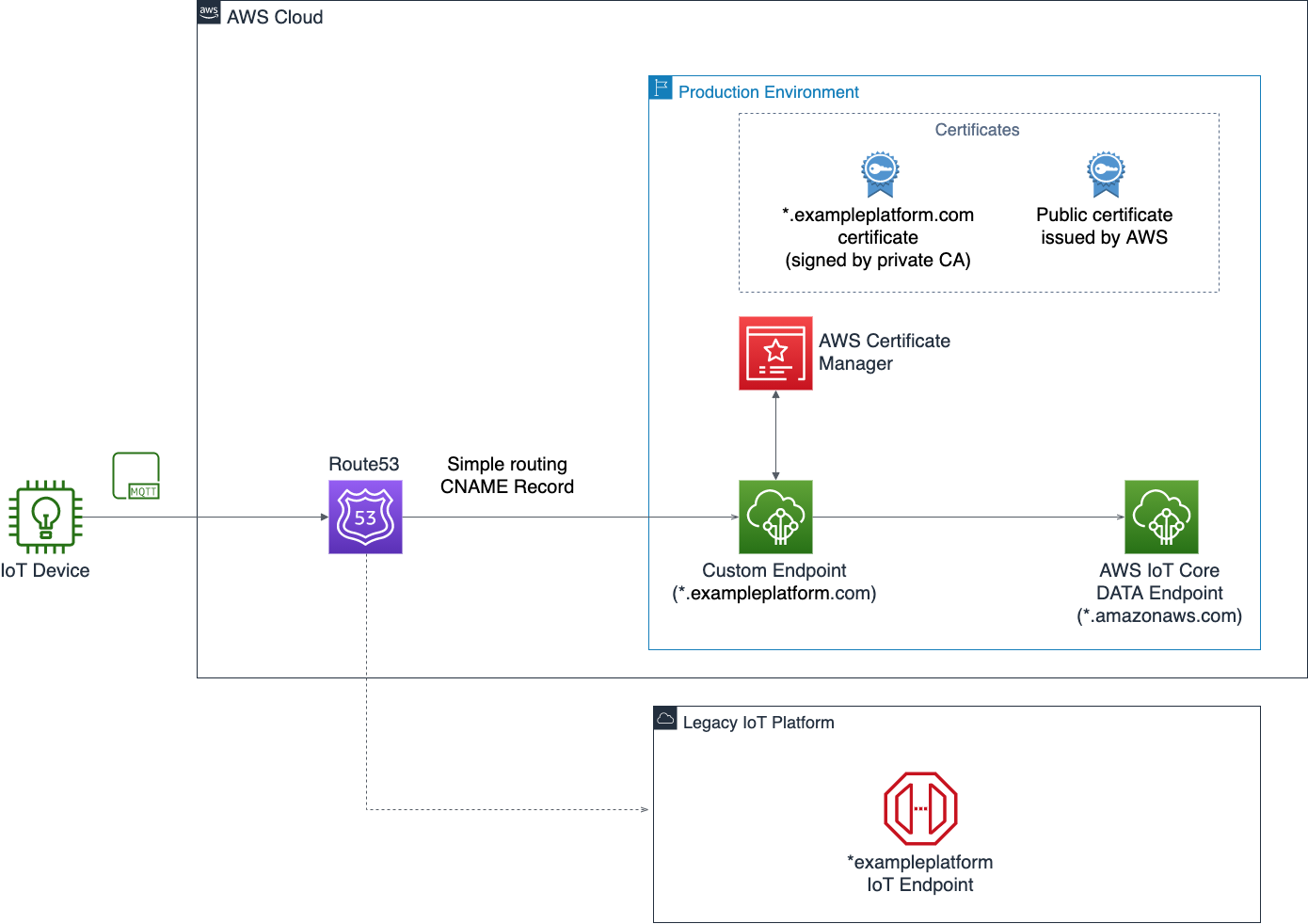
Migrating connected device fleets to AWS with Custom Domains for AWS IoT Core | The Internet of Things on AWS – Official Blog
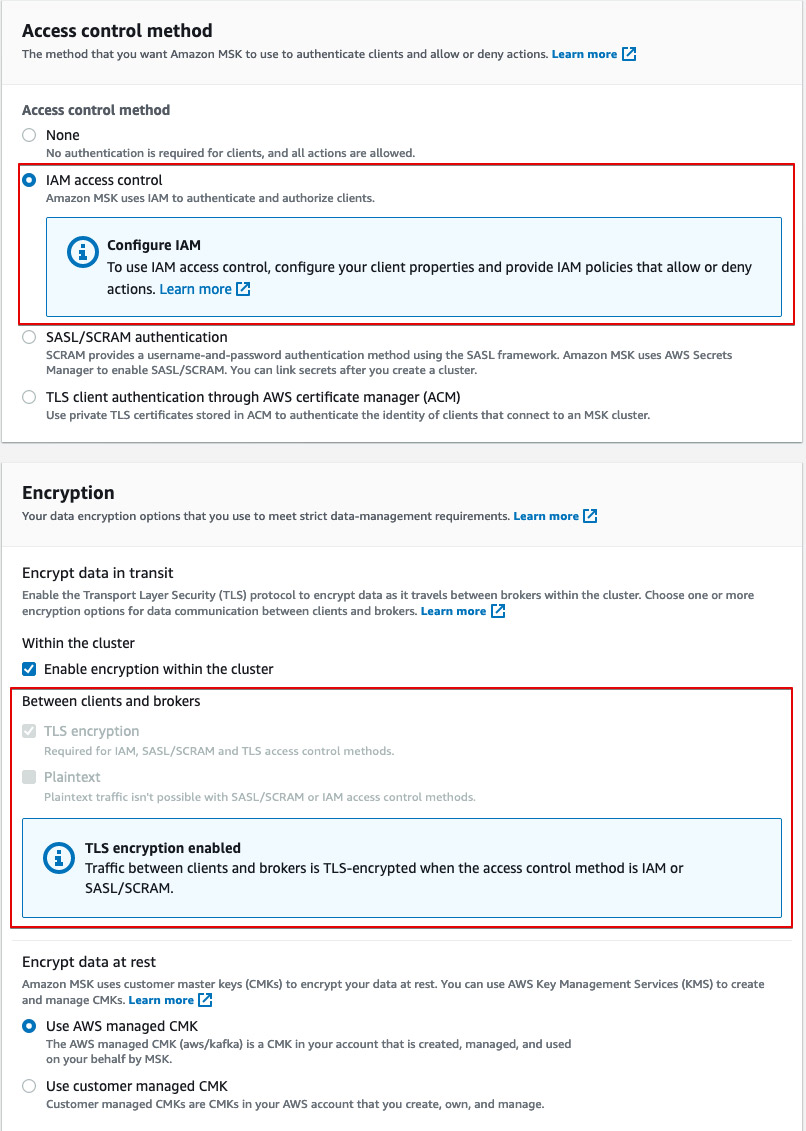
Securing Apache Kafka is easy and familiar with IAM Access Control for Amazon MSK | AWS Big Data Blog
Cracking open the black box of automated machine learning | MIT News | Massachusetts Institute of Technology